Explanation
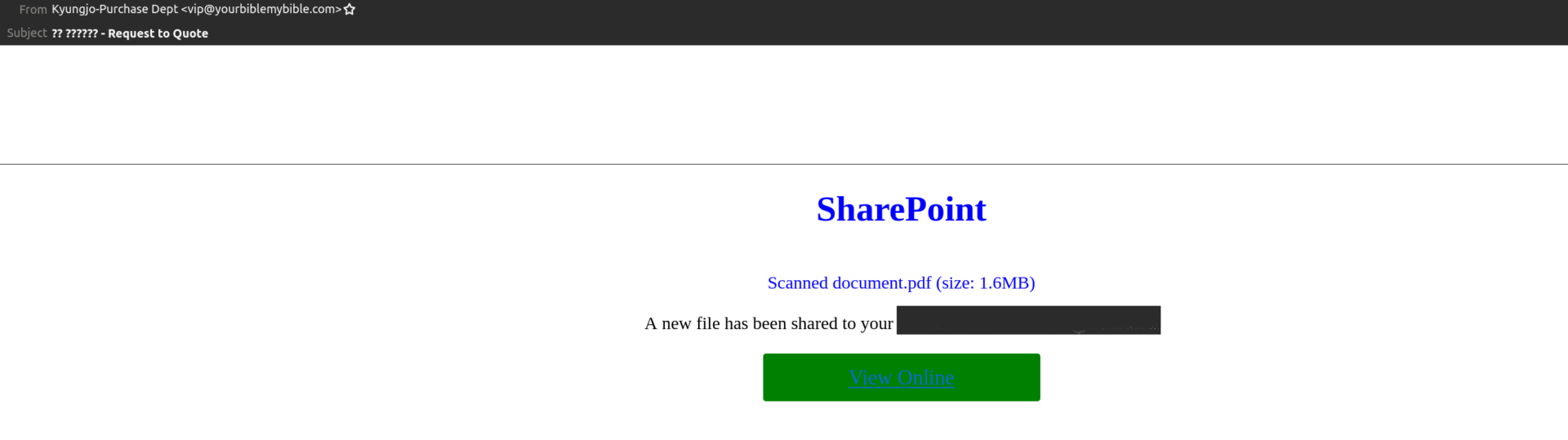
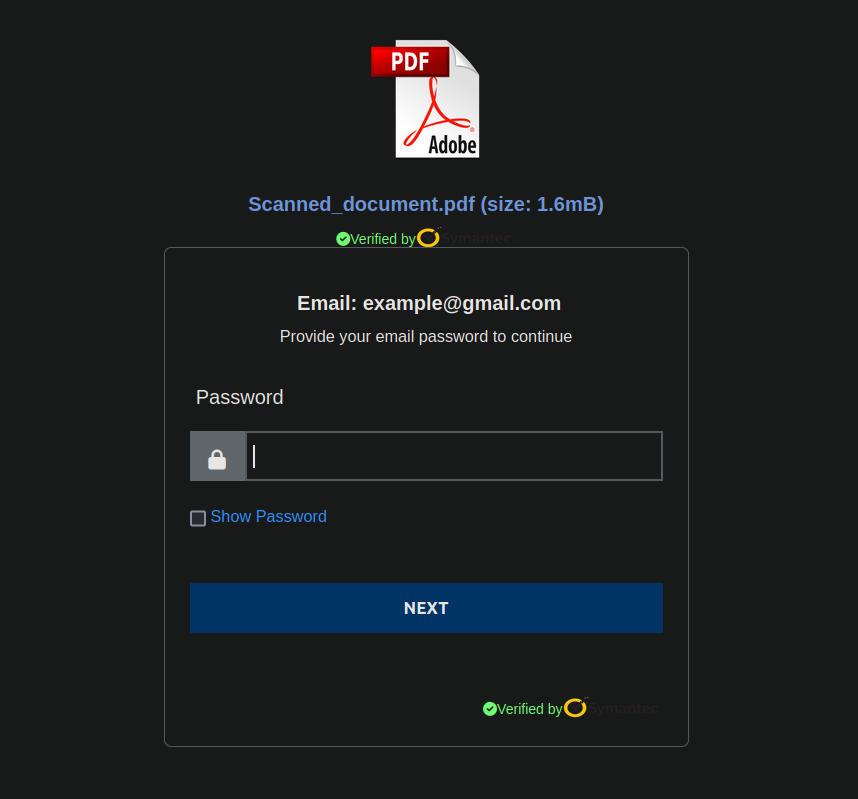
In this phishing attempt, the threat actor sends an email saying that a PDF file is available to be downloaded. The phishing link (hxxps://sfo3[.]digitaloceanspaces[.]com/omdshudhuw0dgw201sei0/%21%24.o.m.%26%26%21/%21%26%21.om.d.%26%24%21.html#example@gmail.com>) makes use of the recipient email address to fill the phishing form.
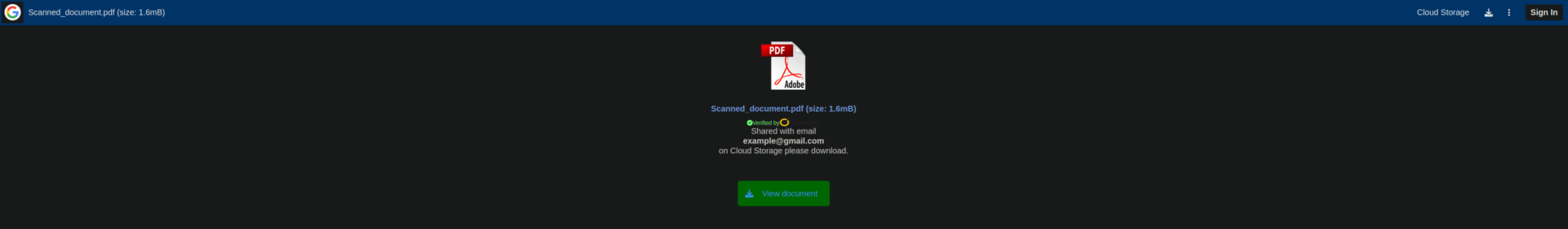
The phishing page detects the domain of the recipient’s email address, and adapts the logo accordingly on the left top-corner. For demonstration purposes, we used gmail.com.
A fake Symantec verification (yellow logo) is also shown to easier acquire the trust of a potential victim. No actual PDF file is available to be downloaded and the threat is limited to phishing only.
Example