Explanation
The goal of this phishing campaign is to steal Netflix, credit card as well as LuxTrust credentials. The entire phishing attempt is conducted in Luxembourgish, however many translation errors have slipped through.
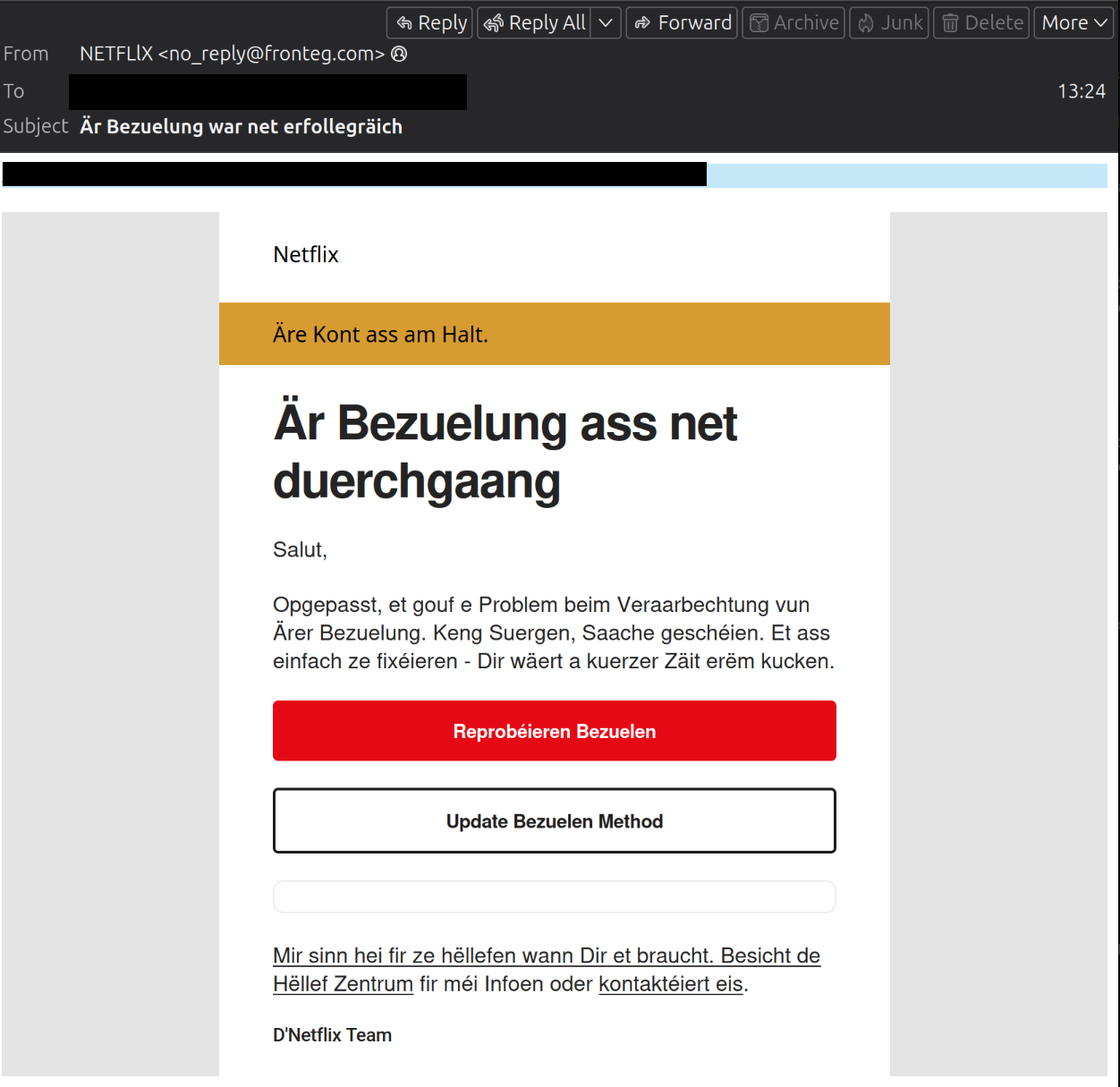
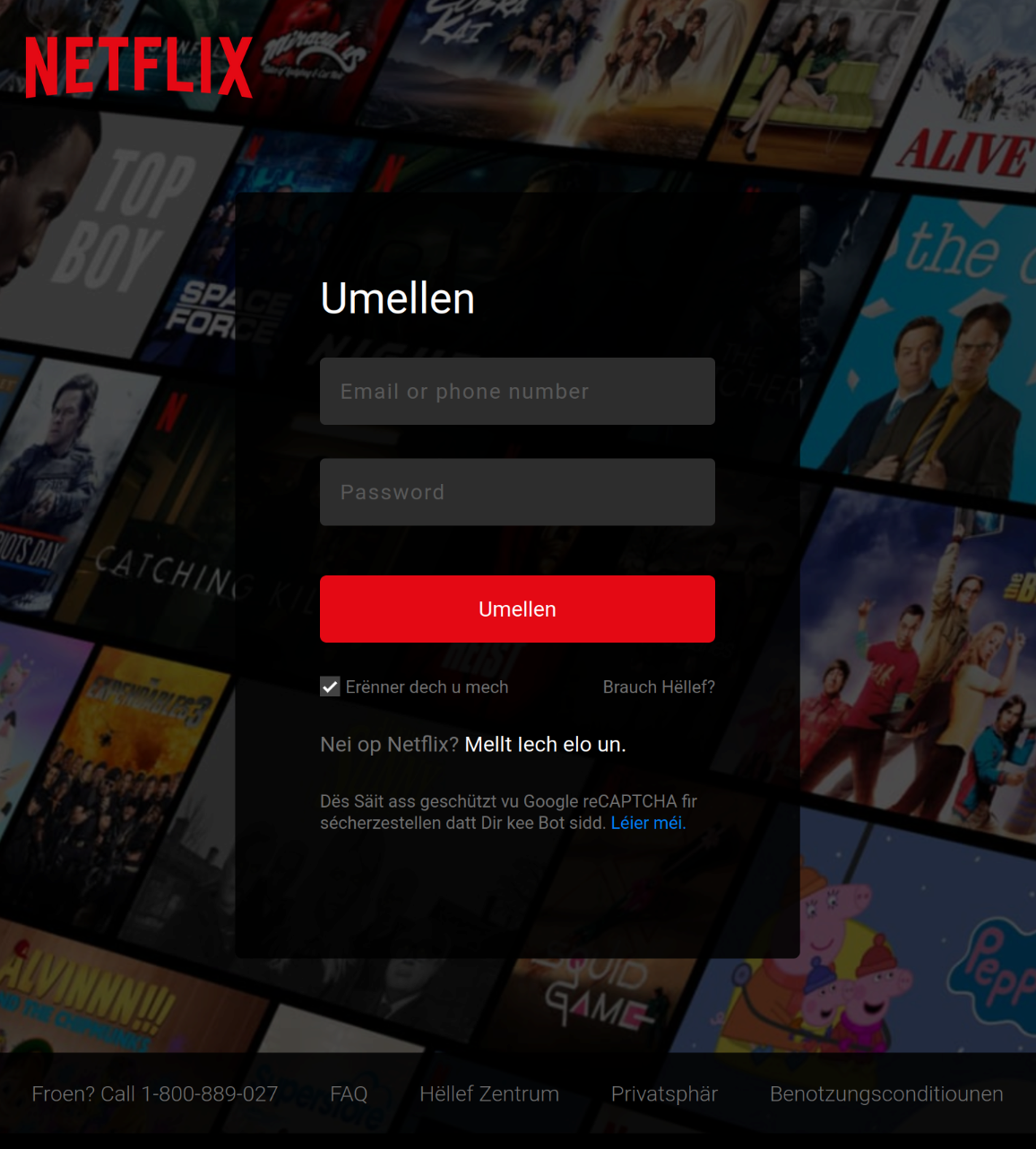
In the email, it is claimed that a Netflix payment did not go through. The message is equipped with several buttons/URLs to click on, but all of them lead to the same landing page. Once there, the user is prompted to enter their Netflix login credentials.
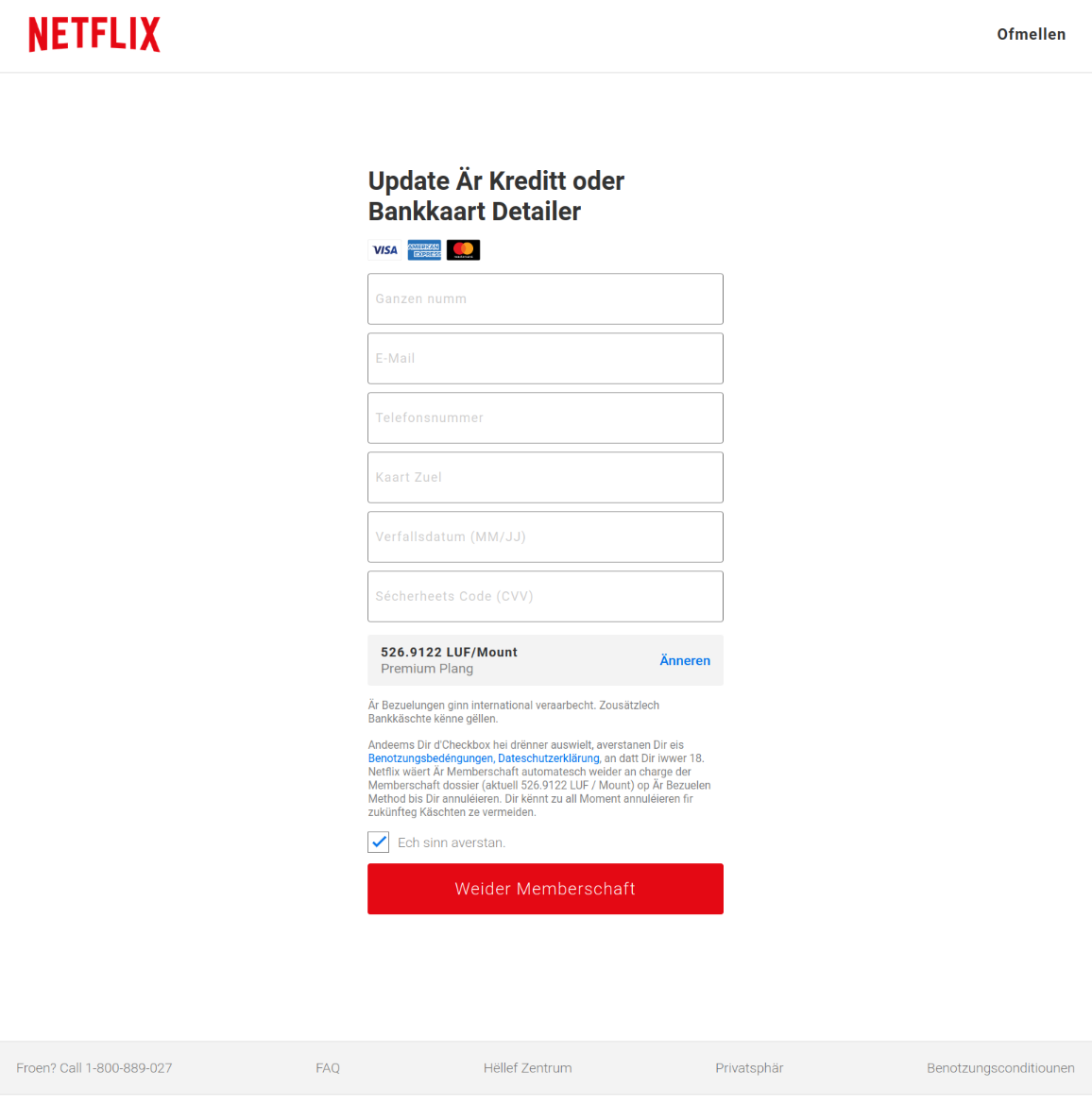
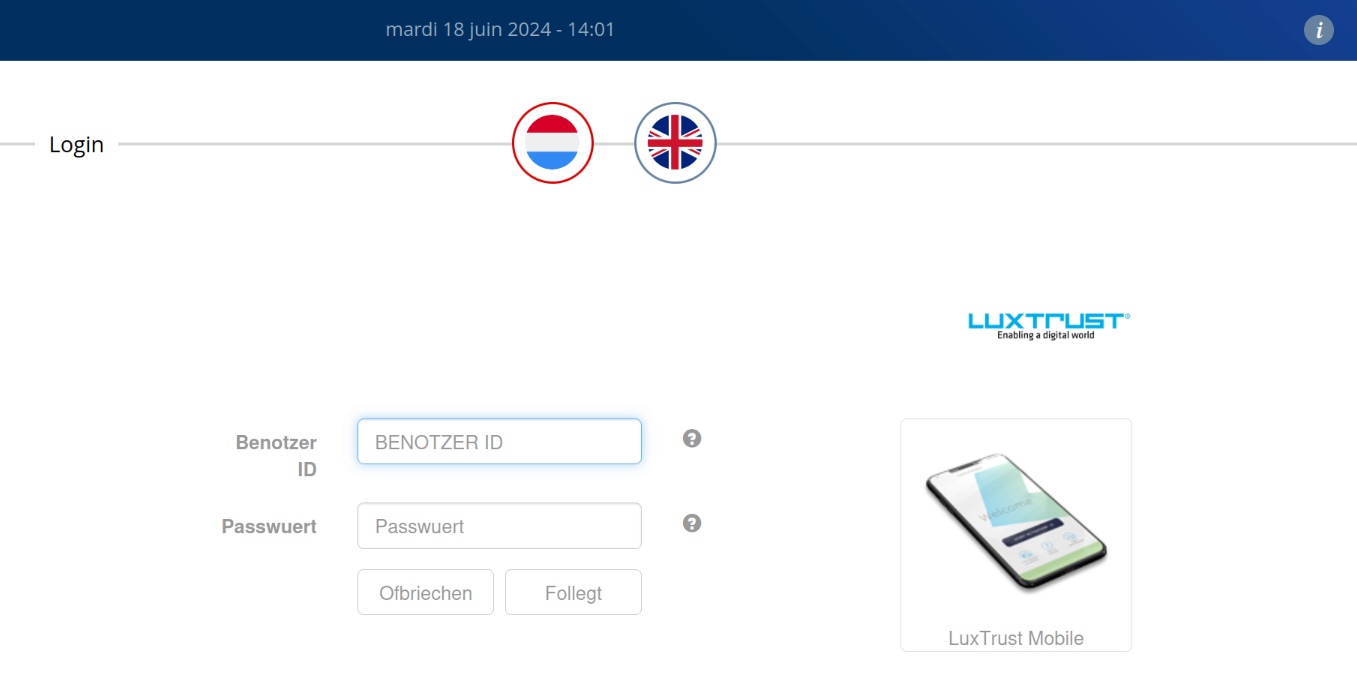
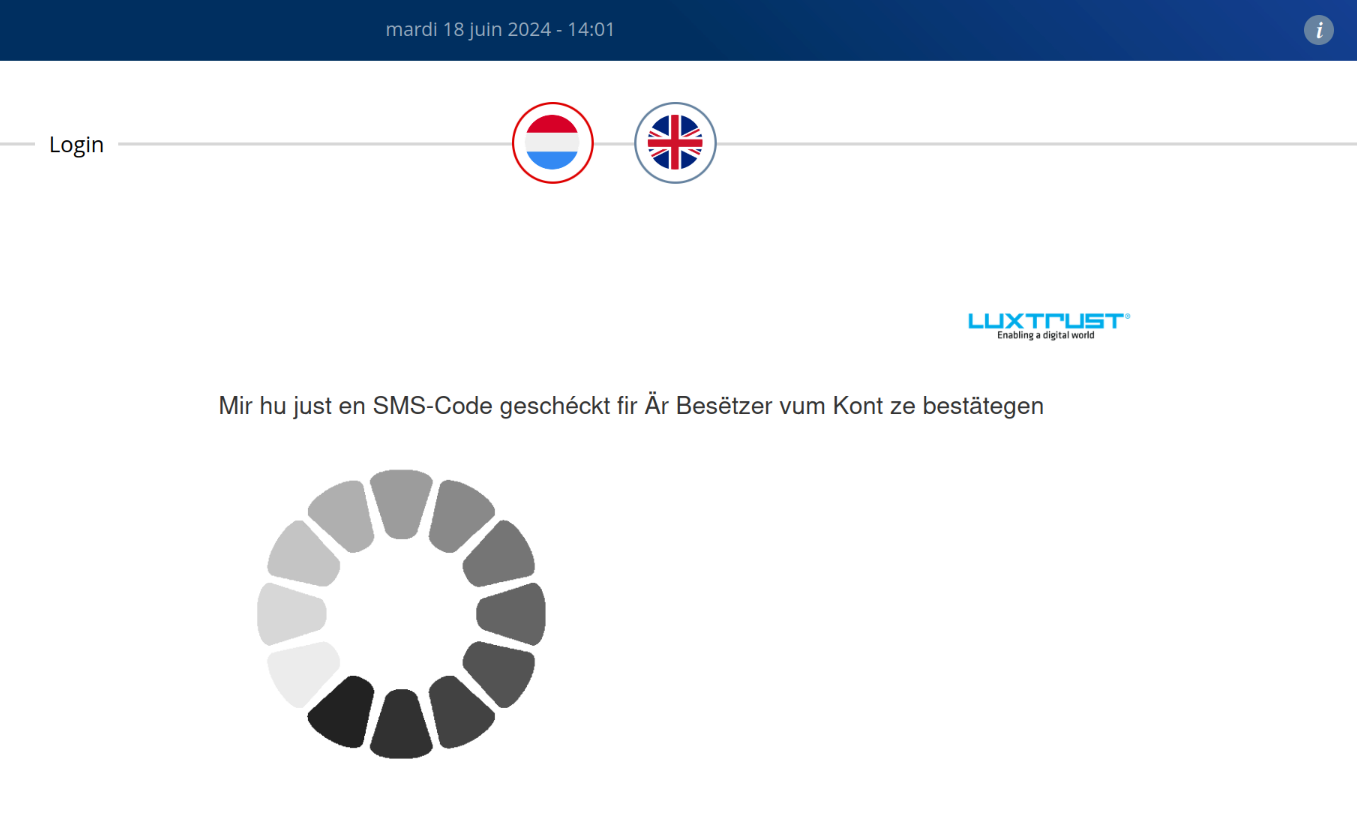
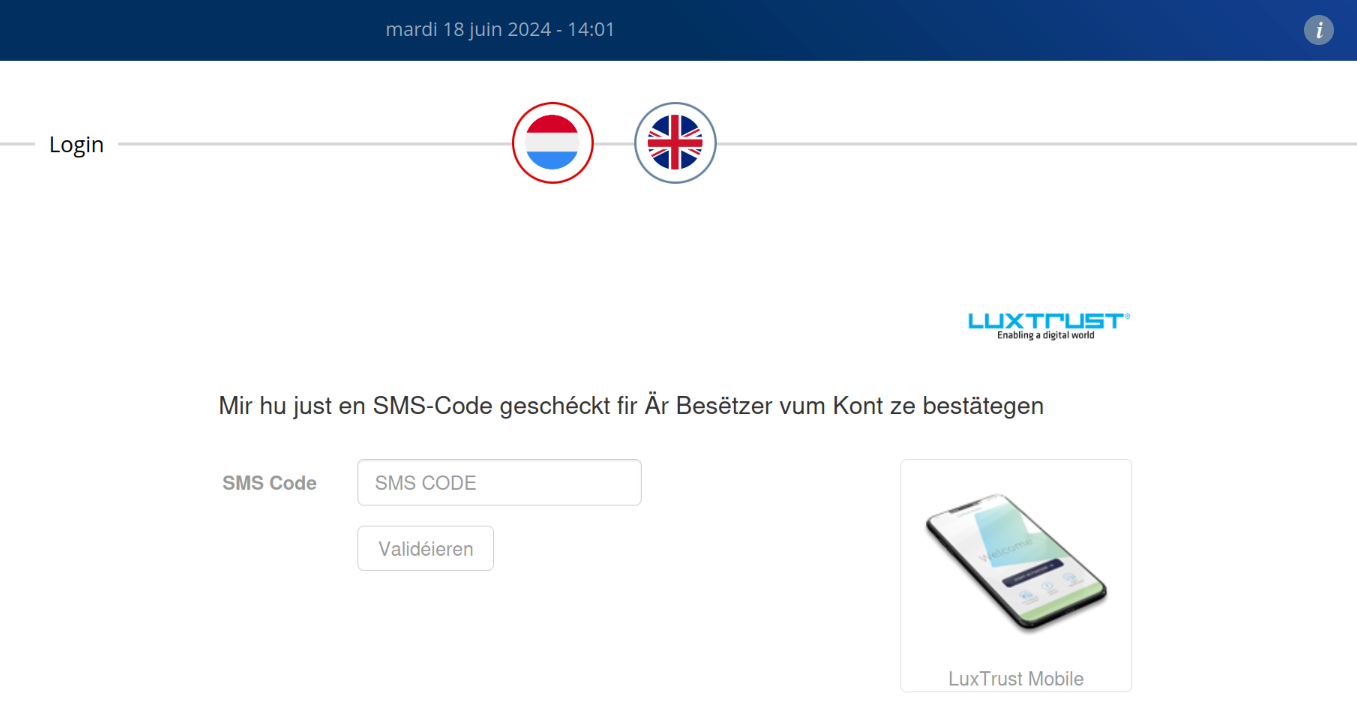
Next, the user is asked to provide some personal data as well as information about their bank card. After that, the system requests the LuxTrust data. Following a brief wait, the user is then supposed to enter an SMS code, which likely stands for the One-Time Password (OTP).
The entire process runs under the malicious domain renderhealth.com .
Example