Explanation
Threat actors are trying to collect Microsoft Exchange credentials of organisations.
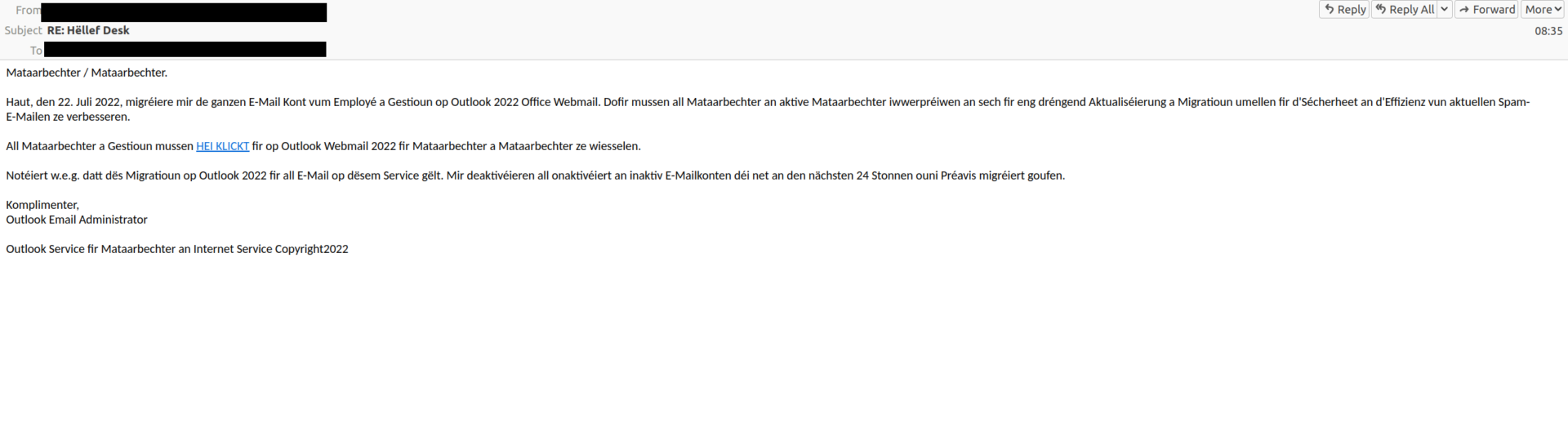
The phishing mail leads the user to believe that the employees email account is migrated and the security settings need to be reviewed, and by clicking on the link the user is redirected to the phishing landing page.
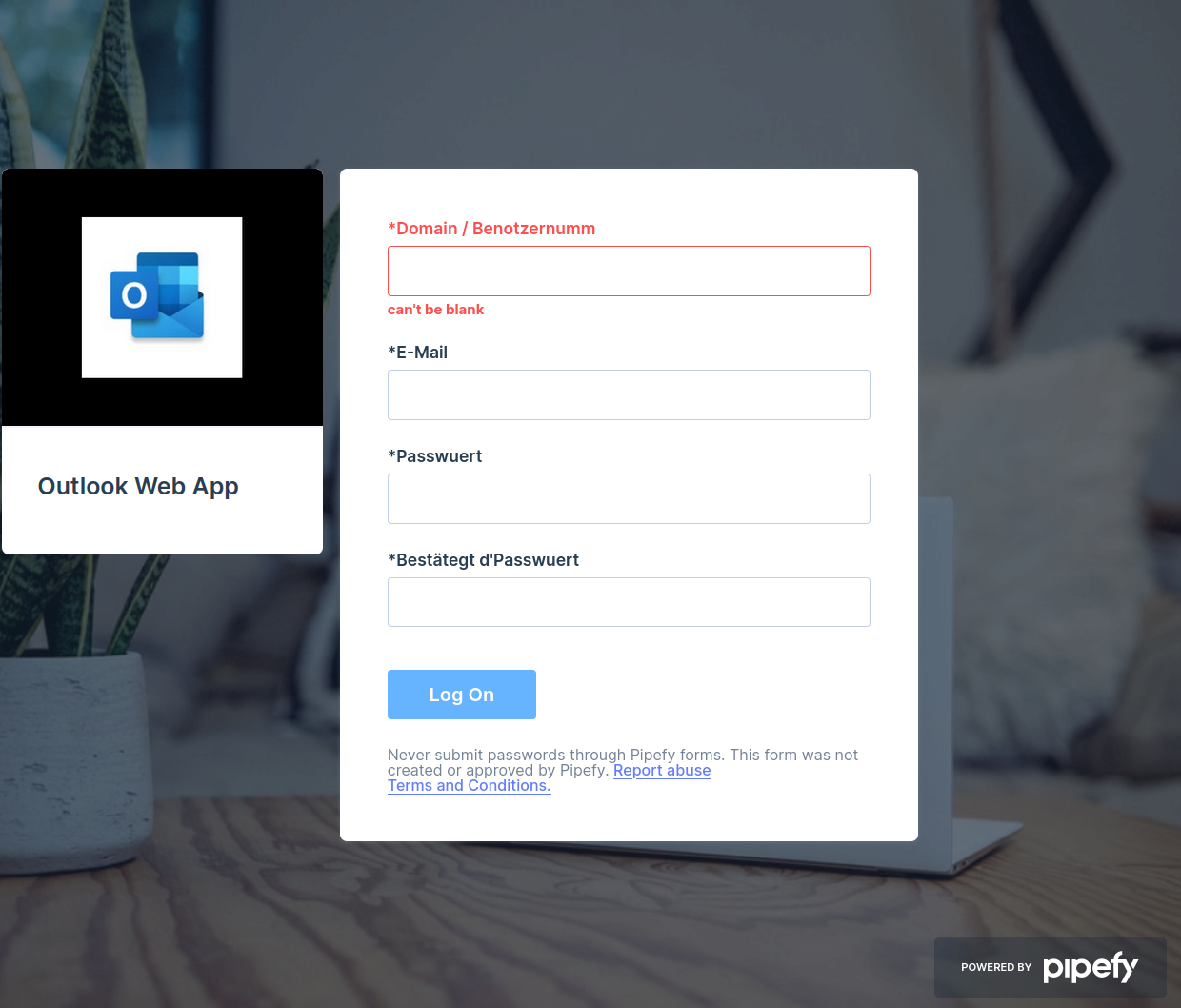
When clicking on the link HEI KLICKT, the victim is presented an input form to collect the credentials.
It’s is easy to recognise that this e-mail is a phishing e-mail because it contains spelling errors and errors in the sentence structure. In addition, on the landing page, one can see the logo of pipefy, which is normally not visible on a legitimate Outlook Web App login form.
Example