Explanation
Threat actors are using a compromised e-mail account of an independent Luxembourgish media company to send phishing e-mails and collect Microsoft e-mail credentials. This makes the emails appear legitimate at first glance, as it seems they come from a known and trusted source.
The attackers are employing a multi-step approach:
Legitimate Dropbox Link: The e-mail contains a Dropbox link to download a PDF file.
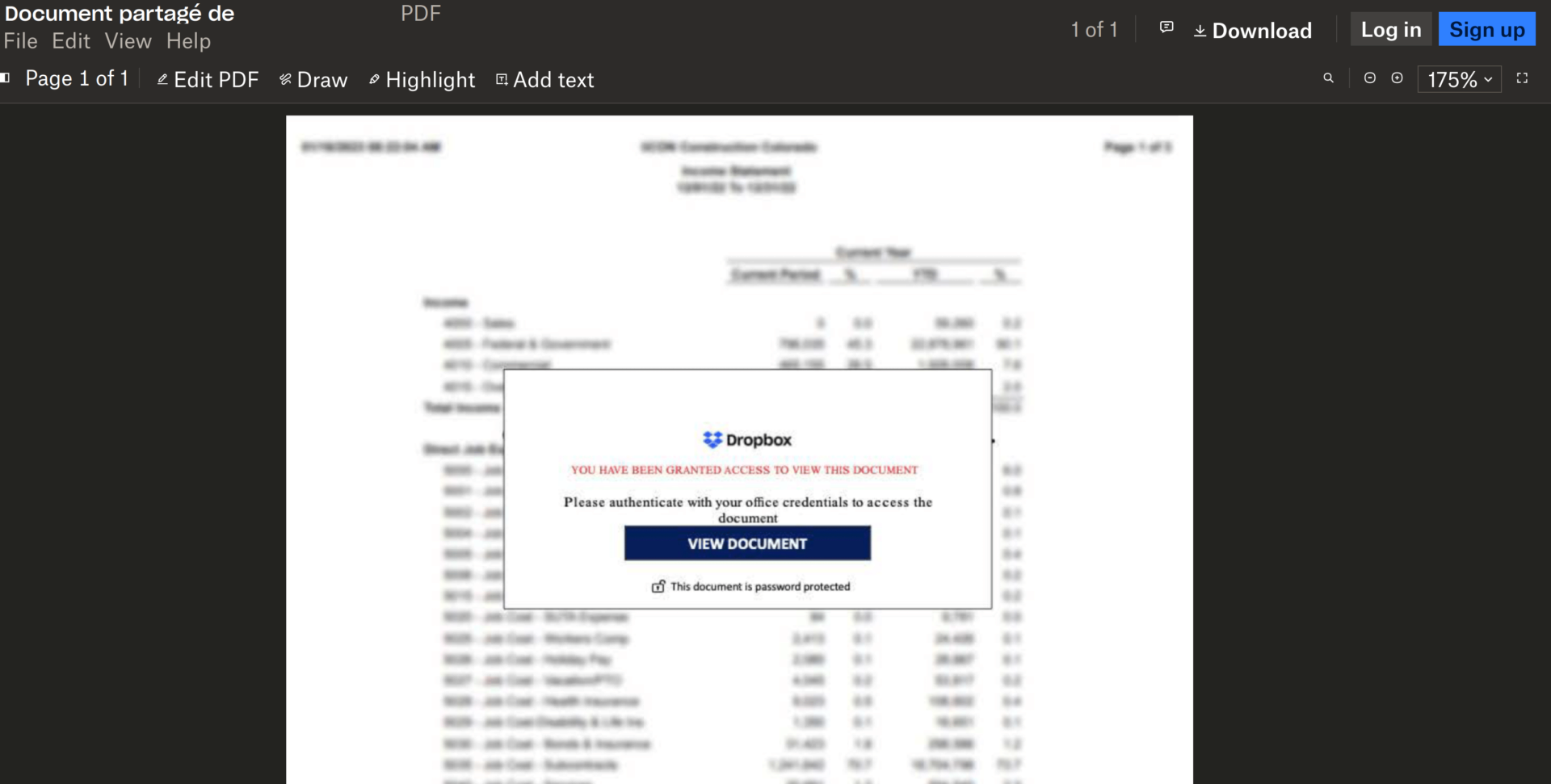
PDF File with Phishing Link: Upon opening the PDF file, there is a phishing link disguised within the document. The PDF file contains content suggesting that important files have been sent, urging users to click on the provided link for further details.
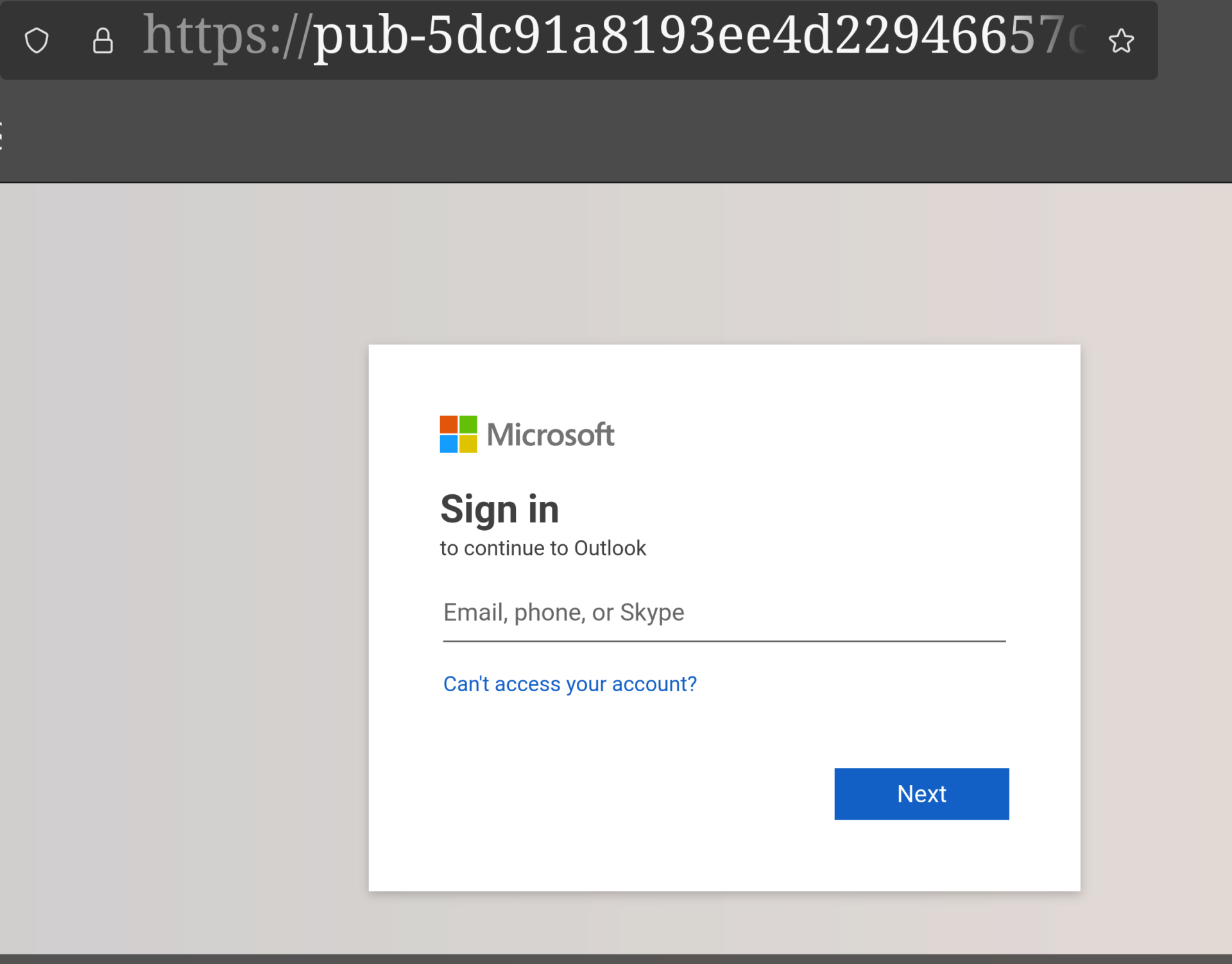
Phishing Landing Page: The phishing link redirects users to a fake Microsoft login page. This fake page closely resembles the legitimate Microsoft login interface, prompting users to enter their username and password.
Example